Ubiquiti UniFi
Ubiquiti UniFi is an enterprise solution for managing wireless networks. The UniFi Controller manages the UniFi infrastructure and can send logs to a remote syslog server via UDP. It acts as a central management point, ensuring that logs from all Ubiquiti access points, including client authentication messages, are forwarded to the syslog server.
NXLog can be configured to collect UniFi logs sent by the UniFi Controller.
Configuring the UniFi Controller
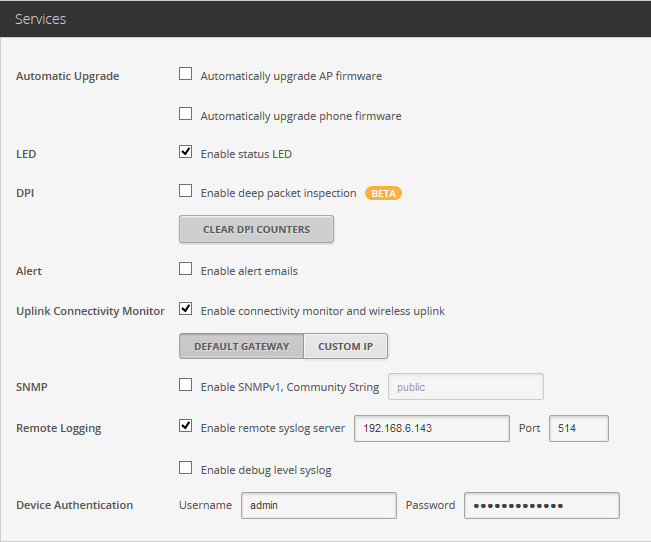
Follow these steps to configure the UniFi Controller to forward logs to a remote syslog server. Refer to the UniFi Controller User Guide for more information on configuration options.
-
Log in to the UniFi Controller’s web interface.
-
Go to Site.
-
Select Enable remote syslog server and specify the IP address and port on which you’ve configured the NXLog agent to listen. See the configuration examples below.
-
If necessary, select Enable debug level syslog.
-
Click Apply to save the changes.
The UniFi Controller sends a lot of low-level information by default, which may encumber log processing and field extraction.
The syslog level can be adjusted for each access point from the UniFi Controller server by changing the syslog.level value in the system.cfg file.
The location of this file varies depending on the host operating system.
For example, the file is located on Windows under C:\Ubiquiti\UniFi\data\devices\uap\<AP_MAC_ADDRESS>.
The controller only forwards access points logs to the remote syslog server.
However, the controller also logs its own events to a local log file, the location of which depends on the host operating system.
On Windows, the file is located at C:\Ubiquiti UniFi\logs\server.log.
If needed, you can collect these logs with the im_file input module.
Collecting UniFi logs
This NXLog configuration uses the im_udp input module to listen for syslog messages on UDP port 514.
<Extension syslog>
Module xm_syslog
</Extension>
<Extension json>
Module xm_json
</Extension>
<Input syslog_udp>
Module im_udp
ListenAddr 0.0.0.0:514
<Exec>
parse_syslog(); (1)
to_json(); (2)
</Exec>
</Input>| 1 | Parses syslog messages into structured data using the parse_syslog() procedure of the xm_json module. |
| 2 | Converts log records to JSON format with the to_json() procedure of the xm_json module. |
{
"MessageSourceAddress": "192.168.10.147",
"EventReceivedTime": "2022-09-20 19:38:55",
"SourceModuleName": "syslog_udp",
"SourceModuleType": "im_udp",
"SyslogFacilityValue": 3,
"SyslogFacility": "DAEMON",
"SyslogSeverityValue": 6,
"SyslogSeverity": "INFO",
"SeverityValue": 2,
"Severity": "INFO",
"Hostname": "192.168.10.147",
"EventTime": "2022-09-20 19:40:44",
"Message": "(\"U7P,0418d6809ce2,v3.7.11.5131\") hostapd: ath4: STA 34:02:86:45:8e:e0 IEEE 802.11: disassociated"
}This NXLog configuration uses the im_udp input module to listen for syslog messages on UDP port 514. It parses each message and uses regular expressions to extract further UniFi-specific fields from the event.
<Extension syslog>
Module xm_syslog
</Extension>
<Extension json>
Module xm_json
</Extension>
<Input syslog_udp>
Module im_udp
ListenAddr 0.0.0.0:514
<Exec>
parse_syslog(); (1)
if $Message =~ / ([a-z]*): (.*)$/
{
$UFProcess = $1;
$UFMessage = $2;
if $UFMessage =~ /^([a-z0-9]*): (.*)$/
{
$UFSubsys = $1;
$UFMessage = $2;
if $UFMessage =~ /^STA (.*) ([A-Z0-9. ]*): (.*)$/
{
$UFMac = $1;
$UFProto = $2;
$UFMessage = $3;
}
}
}
to_json(); (2)
</Exec>
</Input>| 1 | Parses syslog messages into structured data using the parse_syslog() procedure of the xm_json module. |
| 2 | Converts log records to JSON format with the to_json() procedure of the xm_json module. |
{
"MessageSourceAddress": "192.168.10.149",
"EventReceivedTime": "2022-09-20 20:30:13",
"SourceModuleName": "syslog_udp",
"SourceModuleType": "im_udp",
"SyslogFacilityValue": 3,
"SyslogFacility": "DAEMON",
"SyslogSeverityValue": 6,
"SyslogSeverity": "INFO",
"SeverityValue": 2,
"Severity": "INFO",
"Hostname": "192.168.10.149",
"EventTime": "2022-09-20 20:32:11",
"Message": "(\"U7P,0418d6809b78,v3.7.11.5131\") hostapd: ath2: STA 80:19:34:97:62:a6 RADIUS: stopped accounting session 5907CFDD-00000002",
"UFProcess": "hostapd",
"UFSubsys": "ath2",
"UFMac": "80:19:34:97:62:a6",
"UFProto": "RADIUS",
"UFMessage": "stopped accounting session 5907CFDD-00000002"
}